Guidance for improving IIoT-endpoint security
“The number of attacks on industrial endpoints has grown rapidly in the last few years and has had severe effects. Unreliable equipment can cause safety problems, customer dissatisfaction, liability, and reduced profits,” said Steve Hanna, IIC whitepaper co-author, and senior principal, Infineon Technologies. “The ‘Endpoint Security Best Practices’ whitepaper moves beyond general guidelines by providing specific recommendations for different security levels. The document educates equipment manufacturers, owners, operators, and integrators on how to apply existing best practices to achieve the needed security levels for their endpoints.”
We chatted with contributors Steve and Dean Weber, CTO, with Mocana, to learn more…
Smart Industry: Tell us about the white paper.
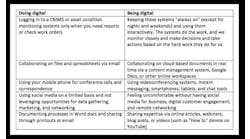
Steve: This is a practical guide for industrial endpoint security designed to help people who are implementing the IIoT. The guide provides simple guidance on what security technologies and approaches are needed so that endpoints can be networked securely. There are multiple target audiences—owner/operators who have industrial systems and are trying take advantage of new IIoT technologies, and system integrators who service the operators, and the manufacturers who build the equipment.
Smart Industry: Why now?
Dean: The Industrial Internet Consortium (IIC) is a relatively new organization. The IIC community provides a standard means of information between industrial manufacturers and operators. There is the recognition that adopting the concepts of industrial networks has not been covered well between verticals or different industries. The IIC facilitates a conversation to make it easier to understand the concepts of security as applied to endpoints. There is a need for education. The operational technology (OT) world has not had to deal with deep embedded security. In the past, engineering processes as well as network detection technologies were heavily relied upon to ensure safety. Holding onto that mindset has made it easy for hackers to gain access to vulnerable equipment. Now there is a growing awareness that we need to rethink how we approach this and focus more on protection vs detection. This IIC ESBP document is a starting point to ensure that devices and data are trustworthy.
Smart Industry: How are applications of IIoT different for endpoints than other industrial elements?
Dean: Part of the problem with endpoints is nomenclature. One endpoint here is not same as the one
there. Is the endpoint a valve? A DCS system? Part of ICS? SCADA? The answer is yes to all of the above. The reality is the endpoint is the place to start. It is the place where data is generated or consumed.
To build secure systems you have to start with a secure subsystem…the devices that are in direct control. This isn’t about logging or analytics; this is about platform security.
Smart Industry: What is a key best practice in the white paper? What most surprises readers?
Dean: People will be surprised that it’s only 13 pages! The beauty of this IIC Endpoint Security Best Practices (ESBP) is that it is easy to absorb. There are clear recommendations for security for several levels of device. There are cybersecurity standards. The goal was to make it easier for OEMs to follow best practices.
Steve: You have to be able to think like an attacker in order to do a good job defending against attacks. The IIC ESBP breaks things down to the fundamentals and provides a simple approach to defend against attacks on industrial infrastructure.
We’re thinking about your digital transformation in 2018...are you? Join us at the 2018 Smart Industry Conference. Learn more here.